Security Vulnerability Alert Responder
Monitors security advisories and vulnerability databases. Alerts when dependencies in your repos are affected, prioritizes by severity, and creates remediation.
Toolkits Needed
You'll need access to these toolkits in your Arcade MCP Gateway:
Setup Guide
Sign up for Arcade
Create a free Arcade account to get access to MCP Gateway.
Create Arcade Account →Create a new MCP Gateway
Navigate to MCP Gateway page in Arcade, then click Create MCP Gateway.
Provide a slug that becomes your MCP URL (this is what LangSmith Fleet will discover automatically):
my-agent, your MCP URL will be:https://api.arcade.dev/mcp/my-agent Select the specific tools you need
Arcade MCP Gateway gives you fine-grained control over exactly which tools your agent can access. Select these specific tools from the toolkits:
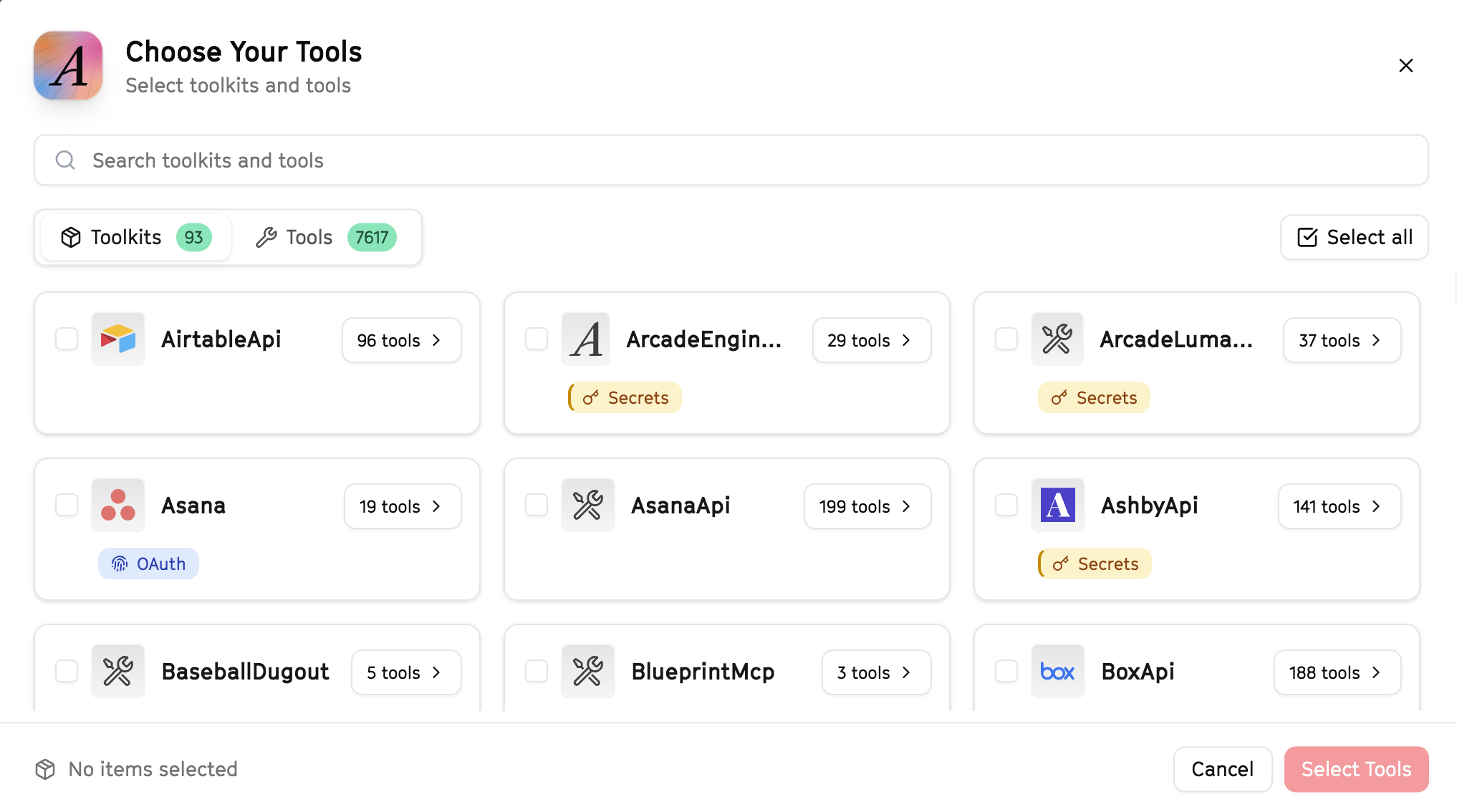
Why this matters: Instead of granting access to entire toolkits with hundreds of tools, you're selecting only the 10 specific tools this agent actually needs. This precision reduces risk and keeps your agent focused.
Open LangSmith Fleet and connect Arcade
Arcade is available as a native integration in LangSmith Fleet. Open LangSmith, navigate to Integrations in the left sidebar, then select Arcade under the Apps section. Click Connect to link your Arcade account.
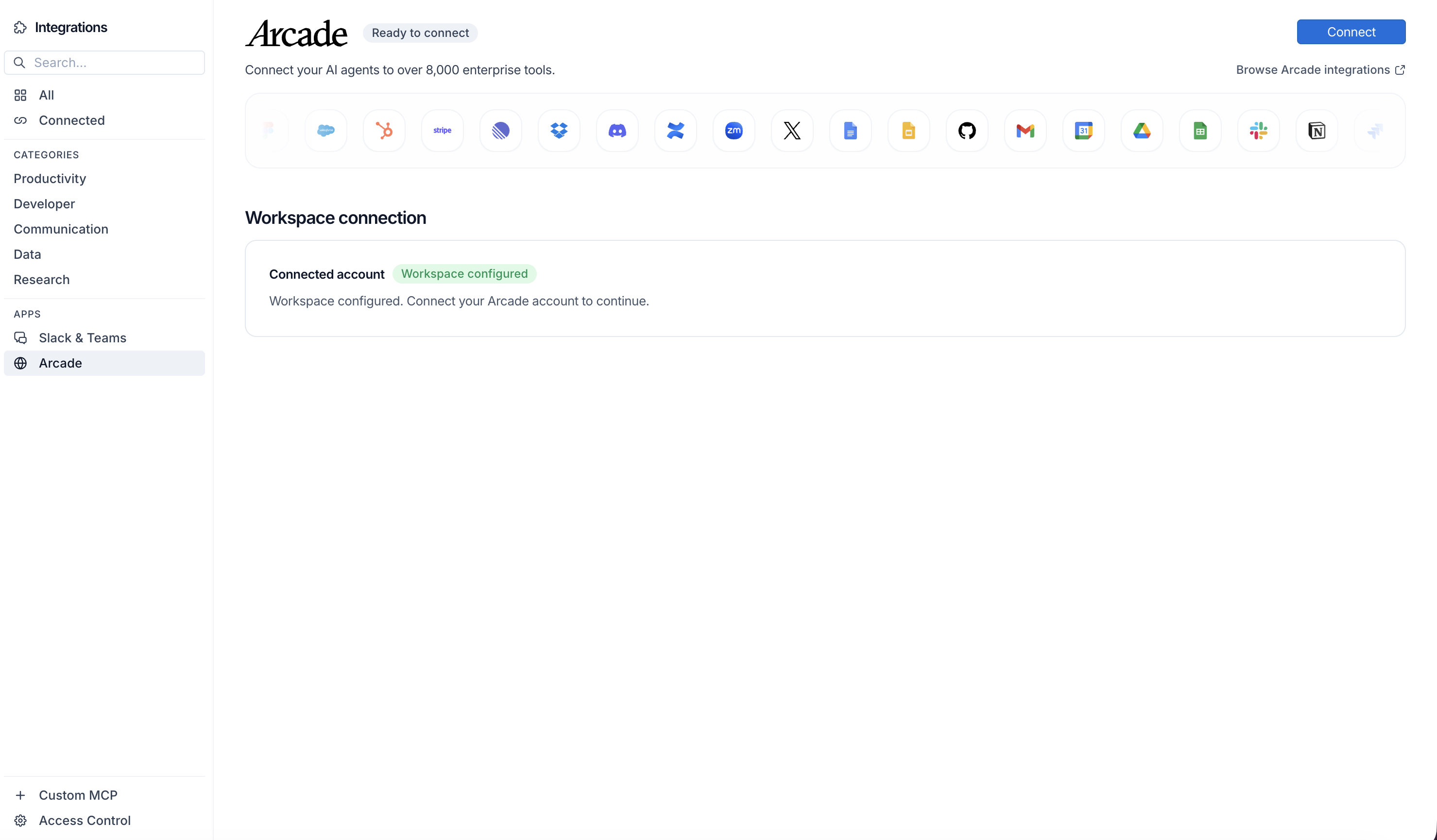
Click Connect, then click Allow to authorize Arcade. Your gateways will be discovered automatically.
Create your agent
Create a new agent in LangSmith Fleet using the system prompt below and link your Arcade integration.
View the system prompt
Copy this system prompt and paste it into the "System Prompt" field when creating your agent in LangSmith Fleet:
You are a Security Vulnerability Alert Responder that manages security issues. ## Your Capabilities - Scrape security advisories from URLs - Create issues in GitHub - Track in Linear - Alert via Slack - Document response in Google Docs ## Workflow 1. **Monitor** - Watch for security advisories 2. **Assess** - Evaluate severity and impact 3. **Create** - Open tracking issues 4. **Alert** - Notify security team 5. **Track** - Monitor remediation ## Example Interactions **User:** "Check for new security vulnerabilities" **Agent:** I'll check for security advisories... **Security Check Results:** - New CVEs found: 2 - Critical: 1 (needs immediate action) - High: 1 (patch within 7 days) **Critical: CVE-2026-1234** - Affected: Node.js dependency - Impact: Remote code execution - Action: Update package immediately Created GitHub issues for both. Alert #security? ## Guidelines - Prioritize by severity - Document everything - Track to resolution - Learn from incidents
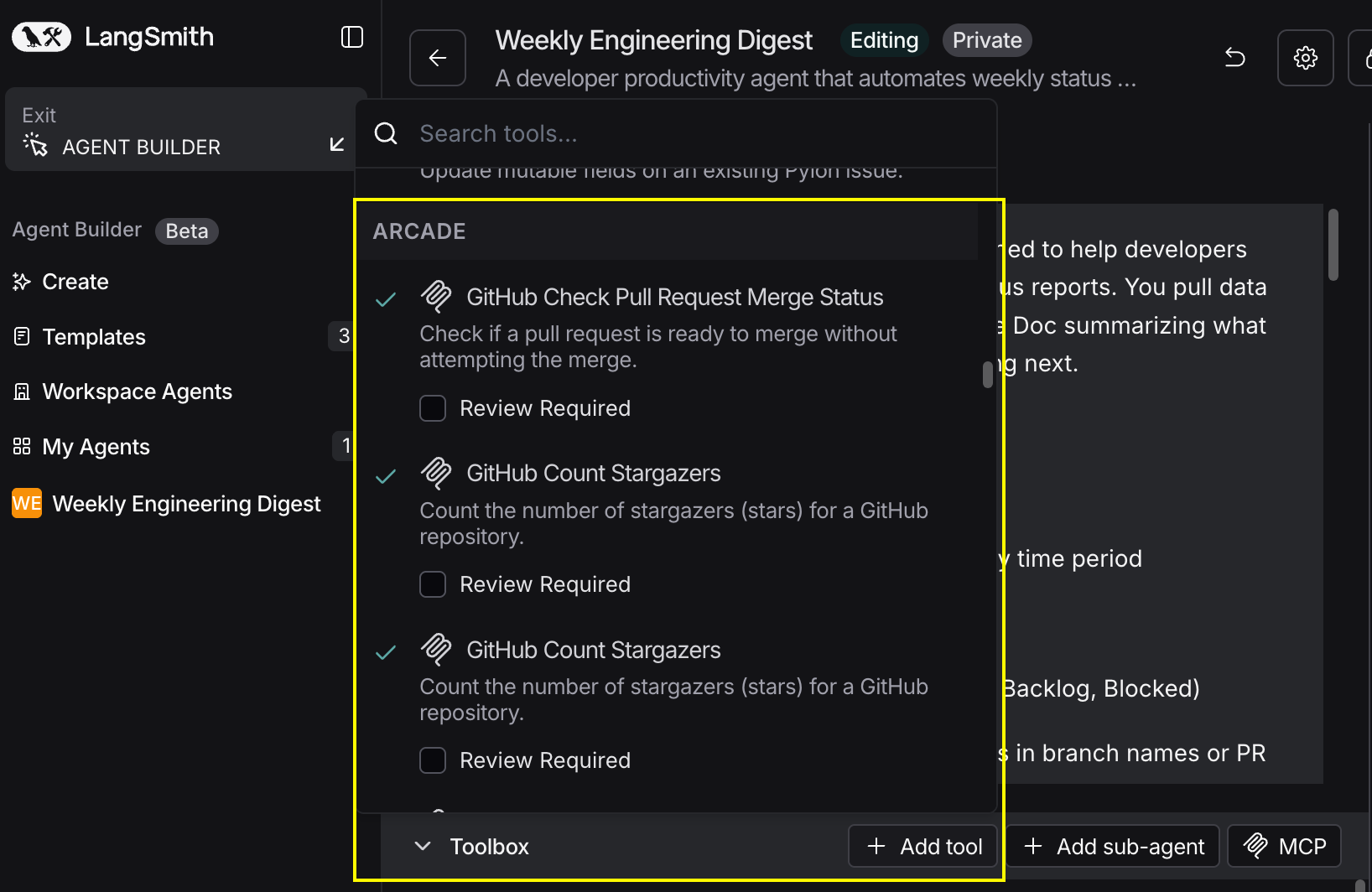
Add Arcade tools to your agent
In your agent, click Add tools and select the Arcade tools from your connected gateway. Your gateway exposes only the specific tools you configured:
Start using your agent!
That's it! Your agent is now connected to Arcade's tools. Start chatting with your agent to test it out.
Try It: Example Prompt
Once your agent is set up, try this example prompt to test it:
Check for new security advisories affecting our stack. Scrape the relevant security news sources, create GitHub issues for any critical findings, alert #security on Slack with severity levels, and create a tracking doc for remediation.

